Microarchitectural Data Sampling (MDS) is a CPU facet vulnerability. Based on Intel, its CPU has some unfastened factors that may be exploited by hackers. This implies taking management of the CPU to have the ability to learn very brief time period knowledge saved in CPU inside buffers. Let’s see the way it works. We may even inform me easy methods to discover out in case your system is affected from this ZombieLoad exploit.
MDS – Microarchitectural Data Sampling
Fashionable Intel processors make use of knowledge storage in its inside buffers, the information being despatched to and from the processor’s cache. The interior buffers of processors are used to chop compute time. For this saving of processor time, knowledge from processors is first saved in inside reminiscence constructed right into a processor like Intel. The information is of the format: TIME, DATA, and IF_VALID columns. It’s to ensure if a bit of knowledge remains to be legitimate at a given time. That is transferred to CPU cache to be used with different firmware or another software program on the pc.
The microarchitectural knowledge sampling (MDS) vulnerability is a technique whereby hackers steal knowledge from processor’s ultra-small buffers in actual time. In every laptop session, knowledge is saved with filters (TIME, DATA, IF_VALID) into these mini-caches. They preserve altering very quick that by the point it’s stolen, its worth (validity too) adjustments. Nonetheless, hackers can use the information even when the information inside processor filters/reminiscence adjustments, permitting them to take management of the machine utterly. It isn’t evident. Issues start when the hacker obtains any encryption key or another helpful knowledge from the mini buffers within the processor.
To rephrase the above, hackers can gather knowledge although the life of knowledge saved is extraordinarily brief. As mentioned earlier, knowledge retains on altering, so hackers should be fast.
Dangers from Microarchitectural Data Sampling (MDS)
Microarchitectural Data Sampling (MDS) would possibly give away encryption keys and thereby achieve management over recordsdata and folders. MDS would possibly give away passwords too. If compromised, the pc could be bricked like in case of Ransomware.
Malicious actors can extract knowledge from different applications and apps as soon as they break into the processor reminiscence. Acquiring the RAM knowledge will not be tough as soon as they’ve the encryption keys. Hackers use maliciously designed net pages or applications to realize entry over processor info.
Worst of all is the shortcoming of a compromised laptop, not realizing that it has been compromised. MDS assault gained’t go away something within the log and doesn’t go away any footprint anyplace on the pc, or community, so possibilities of anybody detecting it are very much less.
Kinds of MDS vulnerabilities
As of now, 4 variants of the microarchitecture are detected:
- Microarchitectural Load Port Data Sampling
- Microarchitectural Retailer Buffer Data Sampling
- Microarchitectural Fill Buffer Data Sampling, and
- Microarchitectural Data Sampling Uncacheable Sampling
This was the longest (one 12 months) interval for which a vulnerability was discovered and stored as a secret till all working system producers and others may develop a patch for his or her customers.
Some customers questioned why can’t they merely disable hyperthreading to guard in opposition to MDS. The reply is the disabling hyperthreading doesn’t present any sort of safety. Disabling hyperthreading will make the computer systems sluggish. Newer {hardware} is being constructed to counter the potential MDS assaults.
Is your laptop weak to MDS?
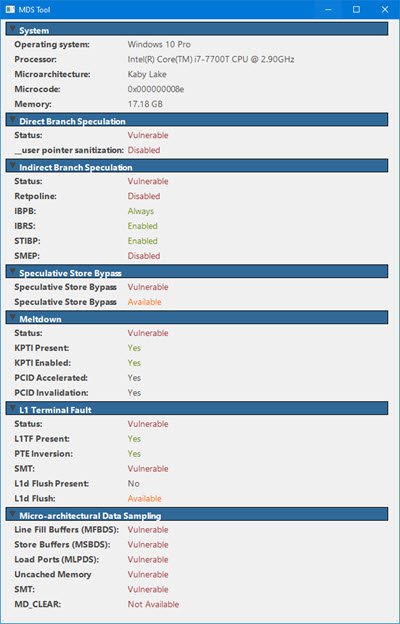
Confirm whether or not your system is weak. Obtain the MDS Instrument from mdsattacks.com. You’ll get a number of different info there.
Learn how to shield computer systems from MDS?
Virtually all working programs have issued a patch which must be used along with the Intel microcode to maintain the vulnerability away. On Home windows OS, the Tuesday updates are mentioned to have patched most computer systems. This, together with the Intel code that’s being constructed into the working system patches, must be ample to forestall microarchitectural sampling (MDS) from compromising your computer systems.
MDSAttacks web site recommends disabling Simultaneous Multi-Threading (SMT), also referred to as Intel Hyper-Threading Know-how, which considerably reduces the affect of MDS-based assaults with out the price of extra complicated mitigations. Intel has additionally supplied CPU microcode updates, and proposals for mitigation methods for working system (and hypervisor) software program. We advocate you put in the software program updates supplied by your working system and/or hypervisor vendor.
Hold your laptop(s) up to date. Replace your BIOS and obtain the most recent system driver on your processor from the Intel web site.
This vulnerability has been patched by Microsoft for his or her Home windows line of working programs. macOS too obtained a patch on Could fifteenth, 2019. Linux has ready the patches however must be downloaded individually for Microarchitecture Data Sampling (MDS).
